PQC SDK
A software developer toolkit for implementing quantum-resistant solutions based on post-quantum algorithms
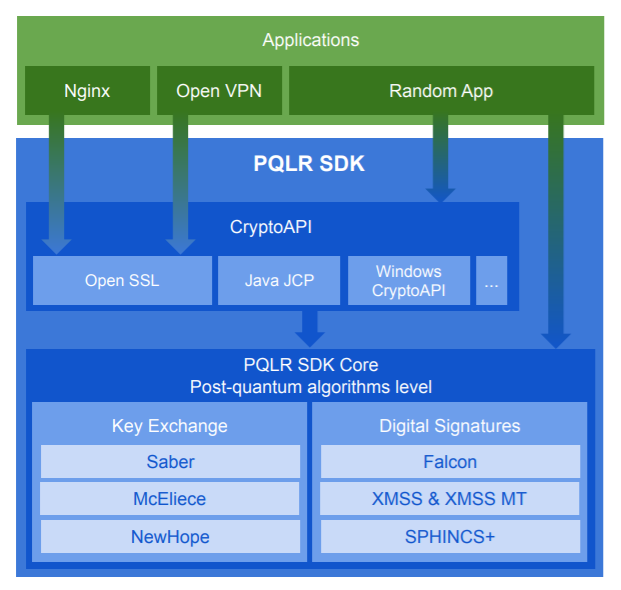
Implementation of leading post-quantum cryptographic algorithms. These algorithms are secure against attacks using both classical and quantum computers. The algorithms are provided as a library and integrated into OpenSSL, enabling their use across a wide range of applications. The library is compatible with all major processor architectures.
Technology stack: C, C++, Java, Kotlin, ES6
Supported platforms:
Implementation of leading post-quantum cryptographic algorithms. These algorithms are secure against attacks using both classical and quantum computers. The algorithms are provided as a library and integrated into OpenSSL, enabling their use across a wide range of applications. The library is compatible with all major processor architectures.
Technology stack: C, C++, Java, Kotlin, ES6
Supported platforms:
- Microsoft Windows® x86_64 (Windows 7 and later);
- GNU/Linux x86_64, glibc ABI 2.19 and later;
- Android 9.0 (Pie) and later for ARMv8-A and ARMv7-A architectures;
- iOS 16 and later.
- Cross-platform and portabilityLinux
on x86-64, ARM v7
Windows
2012+, on x86-64
Android
ARM v7
X86 ARM
Apple
iOS 16+ - ML-KEM
Module-lattice-based
ML-DSA
Lattice-based
SLH-DSA
Hash-based
Hypericum
Hash-based
Saber
Module-LWR based key exchange
McEliece
Code-based
Falcon
Lattice-based
- Integration with OpenSSL
OpenSSL
1.0.2
1.1.0
1.1.1
TLS
1.3
1.2
KEM
EDS
- Reliability and security
Theoretical validation
Implementation testing
ML-KEM (FIPS 203)
ML-KEM (FIPS 203) is a key-encapsulation mechanism (KEM) based on the Module Learning With Errors (Module-LWE) problem over modulе lattices.
ML-DSA (FIPS 204)
ML-DSA (FIPS 204) is a digital signature algorithm based on the Short Integer Solution (SIS) problem on NTRU lattices.
SLH-DSA (FIPS 205)
SLH-DSA (FIPS 205) is a cryptographic scheme based on the cryptographic security of a hash function. The scheme includes algorithms for generating and verifying a digital signature.
The algorithm supports multiple parameter sets, which have a significant impact on performance and signature size.
The algorithm supports multiple parameter sets, which have a significant impact on performance and signature size.
Minimum signature size, kB: 8
Maximum signature size, kB: 48
Hardware test configuration:
Intel® Core™ i7-7700 CPU @ 3.60 GHz
Maximum signature size, kB: 48
Hardware test configuration:
Intel® Core™ i7-7700 CPU @ 3.60 GHz
Hypericum
A Russian digital signature scheme developed by QApp, based on the SLH-DSA (FIPS 205) meta-scheme and the Streebog hash function (GOST R 34.11-2012). The cryptographic scheme includes algorithms for digital signature generation and verification.
The scheme supports multiple parameter sets, allowing trade-offs between performance and signature size.
The security proof is derived from the security proof of SLH-DSA (FIPS 205).
The Hypericum digital signature scheme is in the process of standardization under Technical Committee 26 of Rosstandart.
The scheme supports multiple parameter sets, allowing trade-offs between performance and signature size.
The security proof is derived from the security proof of SLH-DSA (FIPS 205).
The Hypericum digital signature scheme is in the process of standardization under Technical Committee 26 of Rosstandart.
Part 9, page 42
Saber
Saber is a key encapsulation mechanism based on the Module Learning With Rounding (Module-LWR) problem.
Part 6, page 18
McEliece
McEliece is a key encapsulation mechanism based on the problem of decoding a random linear code.
Part 6, page 35
Falcon
Falcon is a digital signature algorithm on the Short Integer Solution (SIS) problem on NTRU lattices.
Part 2, page 10
1. Expert assessment by the mathematical and cryptographic community
While the ultimate limits of quantum computing capabilities remain an open research question, the mathematical foundations underlying the post-quantum algorithms implemented in the PQLR library are among the most extensively studied.
2. Complementarity of algorithms from a mathematical approaches
The cryptographic algorithms implemented in the library are selected to rely on different classes of hard mathematical problems considered resistant to quantum analysis.
These include:
These include:
The Shortest Vector Problem (SVP) in lattices
The Random Linear Code Decoding problem
A searching for the second-preimage resistance, collision resistance, and preimage resistance of cryptographic hash functions
Solving a systems of nonlinear over a finite field
Employing a set of cryptographic algorithms based on fundamentally different mathematical problem classes provides an additional layer of security for information systems if one of the algorithms is compromised.