Secure computation system based on PQCompute software core
Confidential Computing Core
Technology stack: C++, Python, ML
Certificate of State Registration of a Computer Program in the Russian Federation No.2024611073
Technology stack: C++, Python, ML
Certificate of State Registration of a Computer Program in the Russian Federation No.2024611073
Data at rest
Protection of sensitive
data at rest
data at rest
Data in transit
Protection of data
in transit between
public and private network
in transit between
public and private network
Comprehensive Data Protection
Data in use
Protection of data from disclosure even to the system owner performing computations
New protection

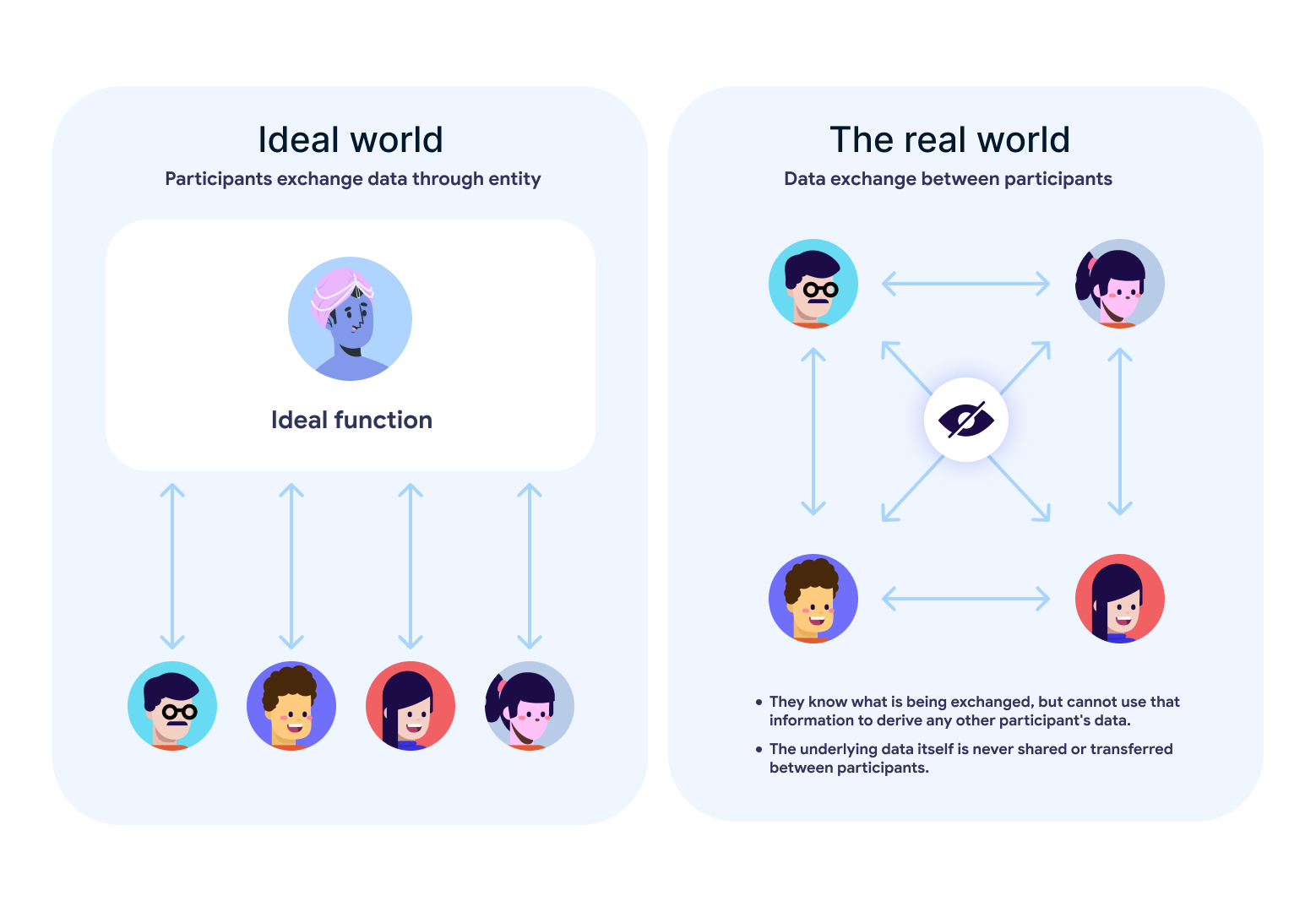
The goal of confidential computing is to provide “ideal-world” guarantees in the real world for secure data sharing and computation
The concept of a trusted third party from the ideal world clearly illustrates the objective of confidential computation: obtaining results from an absolutely trusted, impartial third party that has no incentive or ability to disclose the data. In the real world, this is seems impossible due to conflicts of interest among the parties
This problem can be addressed by secure multi-party computation (SMPC) — a cryptographic protocol enabling joint computation without revealing parties’ private inputs
The concept of a trusted third party from the ideal world clearly illustrates the objective of confidential computation: obtaining results from an absolutely trusted, impartial third party that has no incentive or ability to disclose the data. In the real world, this is seems impossible due to conflicts of interest among the parties
This problem can be addressed by secure multi-party computation (SMPC) — a cryptographic protocol enabling joint computation without revealing parties’ private inputs
Application domains for confidential computing technology
The technology is applicable for any use cases where two or more parties need to perform computations over sensitive data without revealing their secrets

Application domains for confidential computing technology
The technology is applicable for any use cases where two or more parties need to perform computations over sensitive data without revealing their secrets
PQCompute is the core component of a secure computation system
It is based on SMPC technology and enables computation on general-purpose hardware and operating systems. The system is implemented using cryptographic protocols

Certificate of State Registration of a Computer Program in the Russian Federation No.2024611073
Data sharing threat model: comparison of two approaches
- Classical data sharing:
- Significant financial and time costs during data preparation;
- High risk of errors and data leakage during data transfer;
- Reduced accuracy of computations due to data masking.
However, none of the parties is willing to disclose confidential data
- Confidential computing via SMPC protocol (without data disclosure):
- Removes dependency on third-parties for data protection mechanisms;
- Eliminates data masking and filtering requirements for preserving confidentiality;
- Provides resilience against attacks, including quantum computing threats.
Example of protocol operation
QApp serves as а convener of an industry working group on confidential computing aimed at addressing financial sector use cases
Zero Block
Click "Block Editor" to enter the edit mode. Use layers, shapes and customize adaptability. Everything is in your hands.

Tilda Publishing
create your own block from scratch
Working group objectives:
- Align participants’ understanding of the current state of secure computation technology for financial-sector applications;
- Identify technological and regulatory barriers to deploying confidential computing in production over the the next few years, and define approaches to overcome them;
- Align joint efforts of industry participants and regulators in piloting and validating confidential computing technologies;
- Identify synergies between confidential computation technologies and the national project “Data Economy”, as well as related government initiatives